Apple App Store Harbors Dozens of Phishing Apps Stealing Crypto Wallet Keys
In March 2026, security researchers uncovered a coordinated campaign that had placed more than twenty fraudulent applications within Apple's official App Store. These apps, disguised as well-known cryptocurrency wallets, were designed to trick users into revealing their private keys and recovery phrases. Once installed, the apps redirect victims to browser pages that closely mimic the App Store interface, ultimately serving trojanized versions of legitimate wallets.
Background of the Campaign
The malicious activity first came to light when analysts noticed a flood of suspicious apps appearing at the top of search results in the Chinese App Store. The region’s restrictions on many official crypto wallet apps—unavailable to users with an Apple ID set to China—created an ideal hunting ground for scammers. Exploiting this gap, attackers launched apps that used icons virtually identical to the originals, along with deliberately misspelled names—a tactic known as typosquatting—to bypass App Store filters and deceive unsuspecting users.
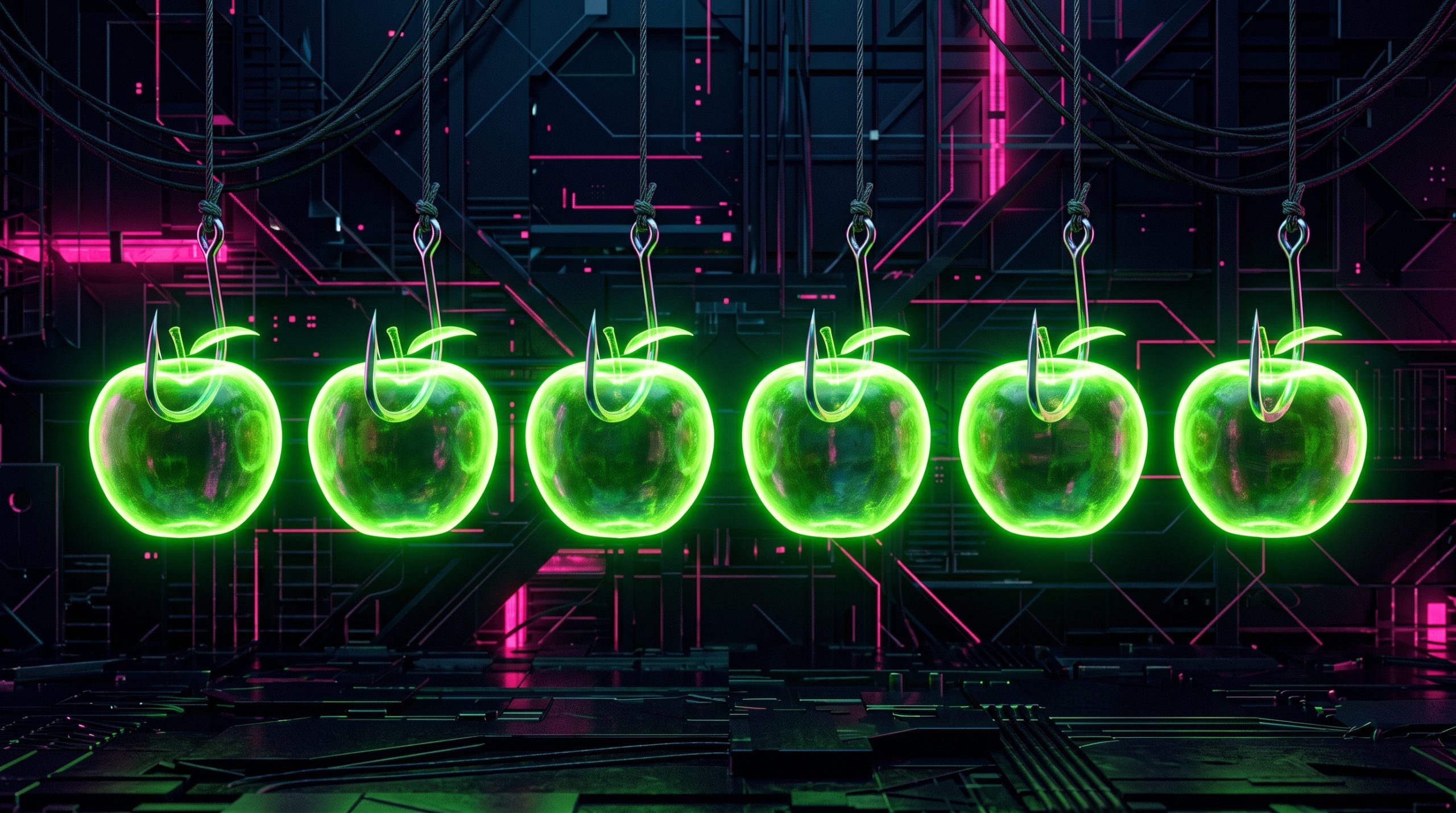
Interestingly, some of the malicious apps bore names and icons completely unrelated to cryptocurrency. However, their promotional banners claimed that the official wallet was “unavailable in the App Store,” directing users to download the wallet through the app itself. This social engineering trick lured victims into trusting the fraudulent software.
According to metadata embedded in the malware, this campaign has been active since at least fall 2025—flying under the radar for roughly six months before detection.
Technical Details of the Attack
Distribution Method
The attack chain begins when a user downloads one of these fake wallet apps from the App Store. Upon launch, the app displays a stub—a functional placeholder such as a simple game, calculator, or task planner—to appear legitimate. Meanwhile, in the background, the app opens a browser page that mimics the App Store product page of the targeted wallet. This fake page tricks the user into downloading a trojanized version of the real wallet application.
The trojanized wallet is built to capture the user’s recovery phrase (seed phrase) and private keys as soon as they are entered. This information is then exfiltrated to the attackers’ servers, giving them full access to the victim’s cryptocurrency funds.
Targeted Wallets
During the investigation, researchers identified 26 phishing apps that specifically mimicked the following popular crypto wallets:
- MetaMask
- Ledger (formerly Ledger Live)
- Trust Wallet
- Coinbase
- TokenPocket
- imToken
- Bitpie
These apps were reported to Apple, and several have already been removed from the store. However, researchers also found a number of similar apps that showed all the signs of belonging to the same threat actor family but had not yet activated their phishing functionality. It is highly likely that these apps are waiting for a future update to toggle the malicious features.
Comparison to Past Attacks
This is not the first time such a scheme has been observed. Back in 2022, ESET researchers documented compromised crypto wallets distributed through phishing websites. Those earlier attacks abused iOS provisioning profiles to install malware, enabling the theft of recovery phrases from major hot wallets. Fast forward four years, and the same core crypto-theft scheme is resurging—now with new malicious modules, updated injection techniques, and a more sophisticated distribution channel through the App Store itself.

Threat Detection and Naming
Kaspersky products detect this family of malware under the following signatures:
- HEUR:Trojan-PSW.IphoneOS.FakeWallet.*
- HEUR:Trojan.IphoneOS.FakeWallet.*
Users are advised to only download wallet apps directly from the official developer websites or trusted sources, and to carefully inspect app names, developer names, and reviews before installing.
Prevention Advice for Users
To protect yourself from falling victim to such phishing campaigns:
- Verify app authenticity – Check the official website of the wallet to find the exact app name and developer. Look for small typos or unusual symbols.
- Avoid click-through downloads – Never download a wallet app via a link that appears inside another app, especially if that app claims the official version is unavailable.
- Use official app stores cautiously – Even though these apps were found in the App Store, they were eventually removed. Always double-check the number of reviews, download counts, and developer history.
- Keep security software updated – Use mobile security solutions that can detect and block known phishing and trojan threats.
Conclusion
The FakeWallet campaign highlights the increasing sophistication of crypto-targeting malware and the creative ways attackers find to bypass App Store security. By exploiting regional restrictions and using typosquatting, the threat actors were able to distribute dozens of malicious apps over many months. While Apple has taken action against many of these apps, the evolving nature of the threat means users must remain vigilant. The fact that similar apps remain in the store—waiting for activation—suggests this is far from over.
Related Articles
- Expanding Retirement Savings: What the TrumpIRA.gov Initiative Means for Workers Without 401(k)s
- Cloudflare Rust Workers Now Immune to Panic-Induced Failures – New WebAssembly Recovery Mechanic Deployed
- Decoding the 2030 Level 5 Autonomy Bet: A Technical Guide
- Spirit Airlines Faces Imminent Shutdown as Federal Bailout Collapses
- Apple Pursues Tariff Refunds and Pledges Reinvestment in Domestic Production
- Apple's AI-Fueled R&D Spending Reaches New Heights: A Q&A
- GameStop’s $55.5 Billion Bid for eBay Sends Shockwaves Through Retail and Tech
- Mastering the CSS contrast() Filter Function: Adjusting Visual Contrast with Precision